The people who get locked out under ‘zero trust’
Security standards like two-factor authentication create barriers for the web’s forgotten users
Editor’s note: Names have been changed throughout this piece to protect the privacy of individuals.
George needs work, but technology keeps getting in the way. Because he’s currently unhoused—sometimes at an Austin-area shelter, but other times in a hand-me-down tent—his phone goes for long periods without a charge or cellular data. A talkative, sixty-ish man with a ready smile, George has known people in his neighborhood for years, including the staff at the public library, where he can use the computers and try to borrow a phone charger. When he can’t, his texts pile up unread, and that means he misses opportunities for small jobs.
Once, George had trouble accessing his email account at a library branch because the email service provider had flagged the login attempt as suspicious, and he was unable to receive text messages at that time to confirm his identity. “Damn thing,” he laughed, recollecting. “Too smart for its own good, huh? Couldn’t prove it was me for the life of me.”
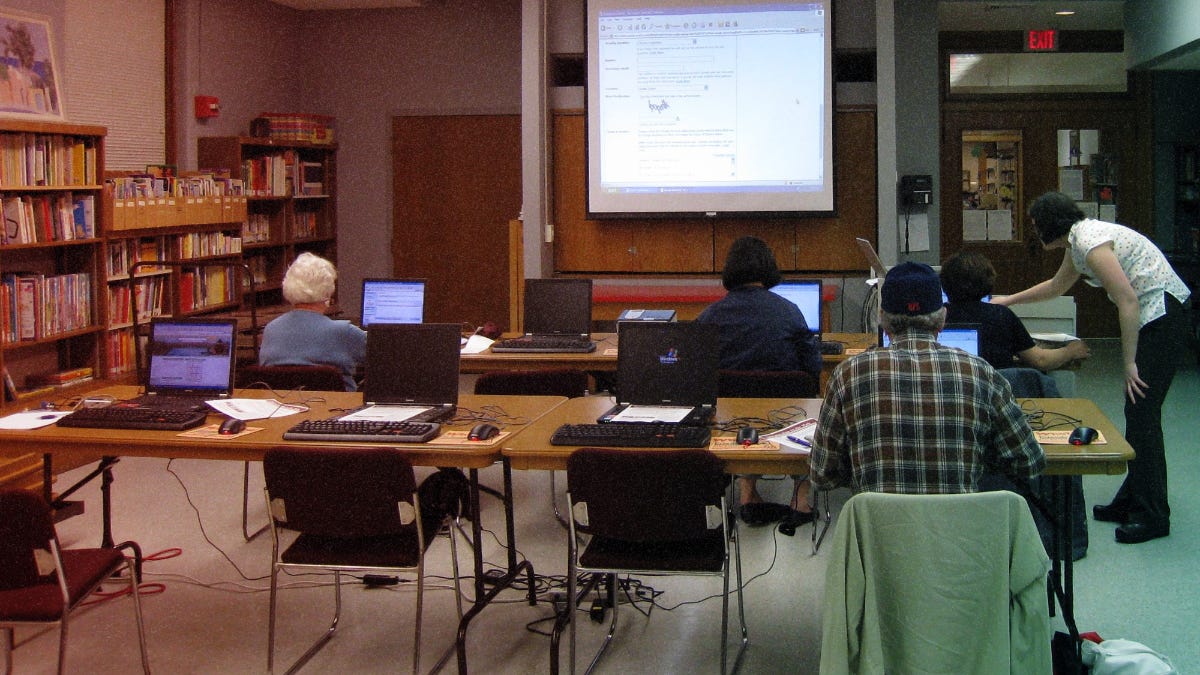
I met George at a local nonprofit that offers free technology classes, like the one on computer basics that George was taking. In the course, students go from learning how to use a mouse and keyboard to browsing the web, creating email accounts and using other common applications like spreadsheets. But as a cybersecurity expert, I was there because I was curious about how a recent evolution in online authentication impacts some of the web’s forgotten users.
In the cybersecurity industry, long plagued by overpromises and hype cycles, the current buzziest buzzword is “zero trust,” a network security paradigm which most users encounter in the form of multi-factor identification. Zero trust is a departure from the traditional network security paradigm, which focuses on defending against cyberattacks at the perimeter of a network and implicitly trusts requests made within the network. When the perimeter model was first implemented, with the invention of the firewall in the late 1980s, computers were stationary machines connected to a network shared by an organization in a single physical location; it seemed only natural that any potential threats would be external.
In subsequent decades, however, as the capabilities and demand for remote access has grown, it has become too easy for attackers to pose as legitimate users. In response to this reality, the zero trust framework treats each request as equally untrustworthy, eroding the notion of a perimeter, but increasing the level of scrutiny on each authentication attempt and each device that attempts to connect to the network.
For example, if an attacker wants access to your online banking account, it’s possible that they could gain direct physical access to your computer, but it’s overwhelmingly more likely for them to gain access through credential theft from thousands of miles away. Therefore, a zero-trust implementation requires not just a username and password, but proof of possession of your personal device, through a code in a text message or recited over a phone call. And since both phone calls and SMS messages have documented vulnerabilities, the more secure methods require either a smartphone or an additional accessory, like a security key.
But this does not work for everyone. For one thing, it assumes each user has a personal device. This alone would already exclude many of the people I met at the computer class—who often simply can’t afford one.
According to Pew Research Center, about three-quarters of U.S. adults own a laptop or desktop computer, and 97 percent of U.S. adults own a cell phone of some kind, with 85 percent owning a smartphone. Smartphone dependency, or reliance on smartphones for most or all online access, has declined from 20 percent in 2018 to 15 percent today, but remains at 27 percent among people with a household income less than $30,000 and 32 percent among those with less than a high school degree. One-quarter of Hispanic Americans are smartphone-dependent, as compared to 17 percent of Black Americans and 12 percent of White Americans.
Most of the students at the class fell into one or more of these categories, including Diane, a Hispanic woman in her mid-forties.
When Diane emigrated to Austin, Texas three years ago, she had a hard enough time navigating English, to say nothing of new technology. She did not have a cell phone and had never used a computer. One of Diane’s sharpest memories was her initial puzzlement at QR codes, which are used by some multi-factor applications to register phones. “I saw it first at the restaurant where my nephew works,” she said. “They got rid of all of the menus because of COVID, but there were no instructions, no anything.”
Diane stayed in a spare room at her sister’s and hoped to find work housekeeping, like she had done previously, or better yet, a custodial job that would provide more regular income. However, when she went to the office of a custodial staffing firm, they told her that they were only accepting online applications, which required her to list both an email address and a phone number. She ended up writing down the contact information of a family member. “That was when I felt kind of stuck, because on the one hand I needed work, but on the other hand, how was I gonna work if I didn’t have money for a cell phone?” Diane told me.
Some families share devices, which creates complications. I met Rosana, a woman in her early fifties who shared a flip phone with her husband for many years. She told me about one particular headache when she hoped to set up an online account with her bank, only to find that doing so required her to register a phone number and verify it through an SMS passcode—but her husband had taken the phone to work that day.
But having a phone of one’s own doesn’t solve everything. Recently, Rosana got a secondhand smartphone at the insistence of her daughter, Rocío. But Rosana felt overwhelmed. “(Rocío) knows how to do everything, but I just see all this stuff come in and it’s like, whoa,” said Rosana, referring to messages she receives over text and on apps like Facebook and Whatsapp. After someone she knew got scammed out of some money, she worried she’d fall victim as well.
Cybersecurity products and platforms have always been aimed primarily at companies and government bodies trying to secure their workforce, for the simple reason that that’s where the money is. According to cybersecurity firm Duo’s most recent State of the Auth report, people who are currently employed are 20 percent more likely to have used two-factor authentication (2FA). In the enterprise market, the typical user profile is a knowledge worker who logs in at regular times, from the same network and the same device. There may be variations, such as during business travel, but most importantly, the user is associated with at least one known device that they consistently use and that can be manually updated to the latest software.
But as more web services begin requiring device-based second factors, it is the most technologically vulnerable who get locked out. In the zero trust framework, the behavior of people like George, Diane, and Rosana might be considered anomalous. The fact that they use shared computers means their IP address constantly changes, which subjects them to more security challenges—putting an extra burden of proof on the individuals least equipped to provide it.
On one hand, such measures improve the security of the account enormously. On the other hand, erecting these barriers present real hurdles for low-digital literacy individuals who are trying to open an email account, a bank account, or otherwise participate in a world that others take for granted. And while this group’s online activity is low by definition, and their accounts usually aren’t high-value targets for hackers, it is these same individuals who stand to lose the most from having their account locked out or taken over by an attacker, since they tend to occupy more precarious positions in society.
Some veterans of the cybersecurity world have already raised concerns. Wendy Nather, Head of Advisory Systems at Cisco Systems, has long decried the state of usability in security, writing in a 2018 blog post, “Security is important, but it shouldn’t be this hard. It shouldn’t require a user to have to learn multiple user interfaces and acquire several apps and accessories just to perform one simple task.” At her 2020 keynote address at RSA Conference, one of the biggest cybersecurity conferences in the world, Nather talked about what she calls the “democratization of security”—the need to shift the focus of industry away from control and toward collaboration, with products and policies that are “designed to be adopted rather than just engineered to be enforced.” It’s a message more of us should heed.
To be clear, zero trust is a big step forward in securing online services. But we can’t give up on protecting those who don’t have a cell phone or a computer. The Covid-19 pandemic has exposed a stark digital divide in our communities, as more people have had their livelihoods determined by whether they can reliably do work over the internet. To democratize this security framework, we must directly address the needs of the personal-device have-nots.
In one promising initiative here in Austin, the city’s Office of Telecommunications and Regulatory Affairs has invested $3.5 million into digital equity-focused nonprofits over the last two decades through the Grant for Technology Opportunities Program, and since 2016 has helped to provide people with refurbished smartphones, tablets and computers through the Community PC Program. Other major cities have started programs to subsidize broadband service and offer digital literacy training. Then-mayor of Chattanooga, Tennessee, Andy Berke, argued last year that to supply such services was akin to paving roads, something that could not be limited to only the wealthy. “We have to start talking about this as infrastructure, not as luxury.”
When I returned to the computer class a few weeks later, students in the computer basics class had already made lots of progress, typing slowly but surely to fill out web forms. Although security was not formally part of the curriculum, their instructor encouraged them to choose long, random passphrases to protect their accounts, and the students navigated through the various applications they had practiced. George was proud to have joined a meeting on Zoom earlier that week, to participate in a conversation hosted by another community organization around providing services to veterans. “I didn’t know how to do that before,” he said, referring to the video call, but “I spoke my truth, and they all heard.”
Maggie Engler is a technologist and researcher focused on security, trust, and safety. She currently builds machine learning for platform health at Twitter and previously did data science at Global Disinformation Index and Duo Security. She lives in Austin.
Design by Josh Kramer.
Photo via Manchester City Library on Flickr, with an Attribution ShareAlike Creative Commons license.